rfid reader identity theft Some security experts have voiced concerns about a phenomenon called RFID skimming, in which a thief with an RFID reader may be able to steal your credit card number or personal information simply by walking within a few feet of you. It’s a scary thought, . See more $1.89Yes it's normal. I use a couple of old credit cards to trigger events around my home. 1. Don .
0 · what is rfid identification
1 · what does rfid theft do
2 · rfid theft hack
3 · rfid theft
4 · rfid scam
5 · how to prevent rfid theft
6 · how do rfid thefts happen
7 · credit card rfid theft
The problem is the version of cards that most hotels and places like that use are not compatible with the NFC reader/writer that most android phones have. I've got quite a few that I've .

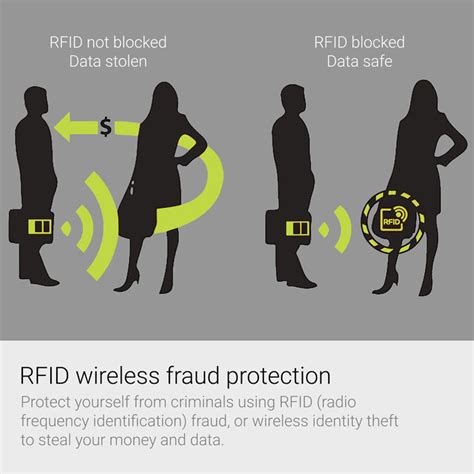
Radio-Frequency Identification (RFID) involves the use of radio waves to read and capture information stored on an electronic chip attached to an object. RFID chips, or “tags,” can . See moreSome security experts have voiced concerns about a phenomenon called RFID skimming, in which a thief with an RFID reader may be able to steal your credit card number or personal information simply by walking within a few feet of you. It’s a scary thought, . See moreWhile RFID skimming should be the least of your worries, it’s important to take steps to protect against the very real threats of credit card fraud and other forms of identity theft. Be proactive with automatic, 24/7 monitoring of your credit report and credit score, so you’ll . See more
What Is RFID Theft? RFID stands for Radio Frequency Identification. RFID theft occurs when someone uses their own RFID reader to trigger the chip in your credit card; a . Some security experts have voiced concerns about a phenomenon called RFID skimming, in which a thief with an RFID reader may be able to steal your credit card number or . What Is RFID Theft? RFID stands for Radio Frequency Identification. RFID theft occurs when someone uses their own RFID reader to trigger the chip in your credit card; a .
RFID cards and tags can be rendered useless by hackers who generate a stronger signal than the RFID reader. This not only disrupts inventory tracking but also causes chaos .Wireless identity theft, also known as contactless identity theft or RFID identity theft, is a form of identity theft described as "the act of compromising an individual’s personal identifying .
It’s where criminals with RFID readers sneak up behind us and scan the credit card or passport in our pocket or bag to steal information they can use for fraudulent transactions or . Passports and some credit cards have RFID chips that allow information to be read wirelessly. An industry has sprung up to make wallets and other products that block hackers . Scam: Card-skimming thieves can make fraudulent purchases with information read from RFID-enabled credit cards carried in pockets and purses. MIXTURE. Examples: .
what is rfid identification
However, there are risks involved — hackers can use this technology to steal data by using RFID readers, writers, and skimmers near people they come into close physical .People often discover their credit card numbers have been stolen by receiving a transaction notification or bank statement showing an unfamiliar transaction. If your card is still with you, . Eva Velasquez, president/CEO of the Identity Theft Resource Center, says that in order to use an RFID reader to steal someone’s data, a bad actor would “have to get very . Some security experts have voiced concerns about a phenomenon called RFID skimming, in which a thief with an RFID reader may be able to steal your credit card number or .
What Is RFID Theft? RFID stands for Radio Frequency Identification. RFID theft occurs when someone uses their own RFID reader to trigger the chip in your credit card; a . RFID cards and tags can be rendered useless by hackers who generate a stronger signal than the RFID reader. This not only disrupts inventory tracking but also causes chaos .
Wireless identity theft, also known as contactless identity theft or RFID identity theft, is a form of identity theft described as "the act of compromising an individual’s personal identifying .
It’s where criminals with RFID readers sneak up behind us and scan the credit card or passport in our pocket or bag to steal information they can use for fraudulent transactions or . Passports and some credit cards have RFID chips that allow information to be read wirelessly. An industry has sprung up to make wallets and other products that block hackers . Scam: Card-skimming thieves can make fraudulent purchases with information read from RFID-enabled credit cards carried in pockets and purses. MIXTURE. Examples: .
However, there are risks involved — hackers can use this technology to steal data by using RFID readers, writers, and skimmers near people they come into close physical .People often discover their credit card numbers have been stolen by receiving a transaction notification or bank statement showing an unfamiliar transaction. If your card is still with you, .
what does rfid theft do
is rfid protection really needed
travelon anti theft rfid protected classic travel safety bag
10PCS NFC Tag NFC Chips Programmable Keychain Ntag215 Chips Timeskey NFC Tags .
rfid reader identity theft|how do rfid thefts happen